Whether yours is a public company that must comply with Sarbanes-Oxley (SOX) guidelines using the COBIT framework or a privately held organization applying good IT audit practices, you’re going to need access to an audit trail at some point.
Maybe you need to prove compliance. Perhaps you’re trying to troubleshoot a processing issue that would explain, for instance, why a customer order did not ship. Possibly you need to provide documentation for why a batch job was changed.
No matter your scenario, providing audit data to your friendly neighborhood auditor that:
1) A process is monitored
2) Exception notification is in place
3) An audit trail exists to facilitate forensics is the new normal for IT
Where’s My IBM i Audit Data?
Using the native IBM i scheduler? If so, where is the audit trail of success/failure logged? You’d have to run multiple commands over QHST, convert the report to a data file, combine the data files, then run another query over the combined data to create a record of jobs starting, run times, end times, and completion codes.
Did a job get added to or changed in the native scheduler? Where is that information? If auditing has not been turned on for multiple objects related to the scheduler, including the *JOBSCD object, then there’s no data to search. If the appropriate auditing has been enabled, then you’d create a program to extract all the pertinent information from the security audit journal to a database file and write a report over the result.
You get the idea. This is no easy task, and programmers have better things to do.
Luckily, Robot has done most of the heavy lifting here by creating multiple audit trails and event logs that are easy to investigate and report on. You can create these reports automatically through our interface by scheduling a command or calling a program and passing the appropriate parameters.
Automatic Audit Trails
Robot software offers built-in audit trails, notification tools, and reports that supply the audit data needed in order to satisfy audit requirements and assist in verifying and summarizing significant aspects of process automation. Here’s what Robot helps you access with ease.
Process Automation
Using Robot Schedule, Robot Schedule Enterprise, Robot Replay
- Processing statistics for each IBM i batch, interactive, and associated Windows, Linux, and AIX tasks submitted (Figure 1)
- Audit trail and notification if a task runs outside of its boundary time (Figure 2)
- Event audit trails for file arrival and directory changes (Figure 3)
- Notification if a critical server is no longer available
- Audit trail of job changes
- Details for all batch activity and terminations
Figure 1 – Job History Reports
The Event Monitoring History reports on files that trigger processes. The event history tracks when a file critical to a process arrives and it’s exact name and location.
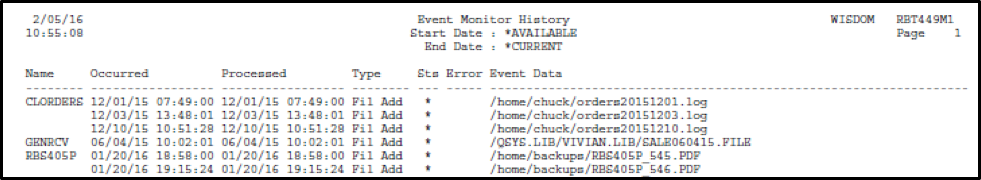
Figure 2 – Event Monitor History Report
Job monitors keep an audit trail and will send notification if a job runs outside its usual run time or doesn’t get a chance to run at all.
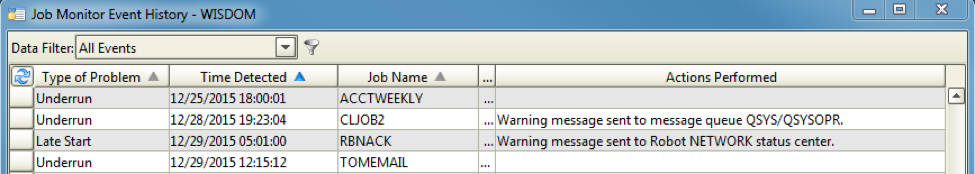
Figure 3 – Job Monitor Log
System Monitoring
Using Robot Console and Robot Alert
- Complete history of all important events logged in QSYSOPR and QHST
- Captured message reply values, who replied, and how long it took to reply
- Summary of your level of message automation and system resource management
Performance Monitoring
Using Robot Network and Robot Space
- Consolidated and summarized issues collected by Robot products on node systems: jobs, messages, backups, performance, disk space
- Detailed performance data reports: disk, memory, and WRKSYSSTS values
- Object growth over time: files, libraries, directories, steam files, out queues, etc.
- Disk usage by object owner or custom categorization
- Reports on largest libraries, objects, directories, IFS files and monitoring information
- Event reports when files, libraries, stream files, and directories exceed a threshold
- Notification when an ASP exceeds multiple threshold utilization levels
- Notification when a library, directory, or file exceeds a size or growth threshold
Backup and Recovery
Using Robot Save
- An up-to-date restoration plan with each backup, created automatically
- Audit trail of what was saved, where it was saved, when it was saved, and what was missed due to locks
Spooled File Report Management
Using Robot Reports
- Summary of the number of reports in online, short-term, and long-term archive
- Reports on who has printed or viewed an online report
One of the standard tools included in Robot automation software is called the Good Morning Report. The report is pre-tooled to include the important detail and summary information needed to verify that processes are good, messages are handled, disk space is under control, and so on.
Audit Data Distribution
An important factor in audit reporting is timely delivery. The audit trail reports can be generated automatically and scheduled to run using Robot Schedule or the databases can be accessed directly using a product like Sequel Data Access if there are very specific reporting requirements. Other tools like Esend or Deliver Now are available to then take that report, convert it to PDF, text, or HTML, and email it directly to the auditor or store it in a pre-defined directory on the network.
Security and Compliance
Whatever the compliance reporting needs, Robot automation software simplifies the process of collecting and reporting on the history and events that take place on your systems, be they batch automation, agent tasks, message and resource monitoring, disk analysis, or save and restore operations.
To further solidify your compliance data collection and reporting the Powertech security toolkit can be added to your portfolio. Powertech provides proactive protection by controlling access to your system, auditing use of powerful profiles, notifying if file data changes outside of defined parameters and will automatically send out reports showing deficiencies in your security configuration of your IBM i.
Combine the Powertech cybersecurity solution with Robot automation software to automatically trigger audits, reporting, or even to automatically archive your IBM i audit data off the system.
Make Your Next Audit Easy
Robot automation software makes it easy to capture and report on the required audit parameters no matter what your industry or compliance need. Start with your most pressing need, add additional automation or monitoring tools as your audit project matures, and then expand on your cybersecurity. Passing your next audit will be a breeze.


