Leverage Powertech RSA SecurID Agent for IBM i
Powertech RSA SecurID Agent for IBM i brings the full functionality of market-leading RSA SecurID two-factor authentication to IBM i.
Secure Transactions
Adding an additional layer of control to systems and applications gives employees, customers, and partners confidence that their sign-on is secure.
Meet Industry Requirements
Securing remote and non-console administrative access via multi-factor authentication is now required for PCI DSS compliance.
Get Started Easily
As a targeted implementation, extra controls are only applied where needed, minimizing business disruption, cost, and time to get up and running. The modern, intuitive interface makes it easy for users to get started.
Features

Unique Password Generator
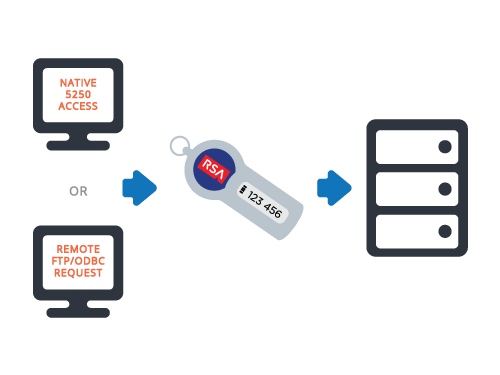
Increase your security by requiring users to authenticate their identities using two different factors: something they know (a password or PIN) and something they have (an authenticator).
Powertech RSA SecurID Agent for IBM i works with RSA SecurID hardware and software-based tokens to request dual-factor authentication at the access points you specify. The software generates a one-time password every 60 seconds, coupled with a user’s PIN, which provides that added security layer.
Phased Implementation
Implement Powertech RSA SecurID Agent for IBM i quickly and easily. This software allows for a phased implementation, so you can enroll users one by one, minimizing hassle and making it easy to get started.
With Powertech RSA SecurID Agent for IBM i, there is no need to redevelop in-house or third-party applications. The software is ready to go when you receive it.

Targeted Authentication
Protect corporate assets and demonstrate compliance with security requirements through targeted authentication. You can enforce a security check anywhere in a program or menu—wherever you want to increase network security.
The ability to require two authentication factors makes it easy to enforce a robust user access policy and report on it to comply with security regulations.
Get Started
Give users the confidence that their transactions are secure, while creating an extra security later to protect corporate assets from unauthorized access. See how Powertech RSA SecurID Agent for IBM i works with a free demo.
In just 10 minutes, find out where your IBM i security currently stands with a free Fortra Security Scan. We’ll evaluate your system’s vulnerabilities and suggest steps you can take to protect your critical data. It’s quick and easy, with no obligation to you.
