THE PROBLEM
Organizations that still take a perimeter-only approach to their data security are increasingly vulnerable to security breaches – because that perimeter no longer exists. Today’s organizations need to share data in a variety of ways, with a variety of people, to efficiently collaborate and do business. This data exchange is happening in complex hybrid IT environments, at an unprecedented pace – not to mention in a world of growing privacy regulations that demand compliance. Human error, workflow bottlenecks, cumbersome systems, and a lack of system integration can leave organizations, and the information they need to protect, vulnerable.
In a survey of CISOs worldwide, security leaders cited data visibility as their biggest cybersecurity weakness – and the majority agreed cyberthreats have become fiercer than they were the previous year.
All these factors introduce the risk of sensitive information getting into the wrong hands. Organizations who want to protect their data, finances, and reputations must act in the face of these challenges.
THE SOLUTION
A state-of-the-art data security solution must:
- Understand and classify files that contain sensitive data
- Detect and prevent leakage of this sensitive data outside the enterprise
- Secure and protect sensitive data that must be shared inside and outside the enterprise
Data protection also requires solutions that can be integrated and deployed quickly, with minimal impact on internal resources and productivity.
WHY Fortra
While many security tools still focus on a perimeter approach, we understand the perimeter no longer exits and aim to protect data wherever it resides throughout its journey. Fortra offers automated,-to-end data-centric security for unstructured data. Regardless of how it moves or where it lives, data is identified, secured, and protected throughout its journey.
Our best-of-breed technology is modular so organizations can choose parts to satisfy their most critical need. We’ve also built meaningful integrations between the suite so customers can deploy solutions in tandem for added benefit. And as a single vendor for all your data security needs, you can rely on us for the expertise and technical support you need, when you need it.
How We Help
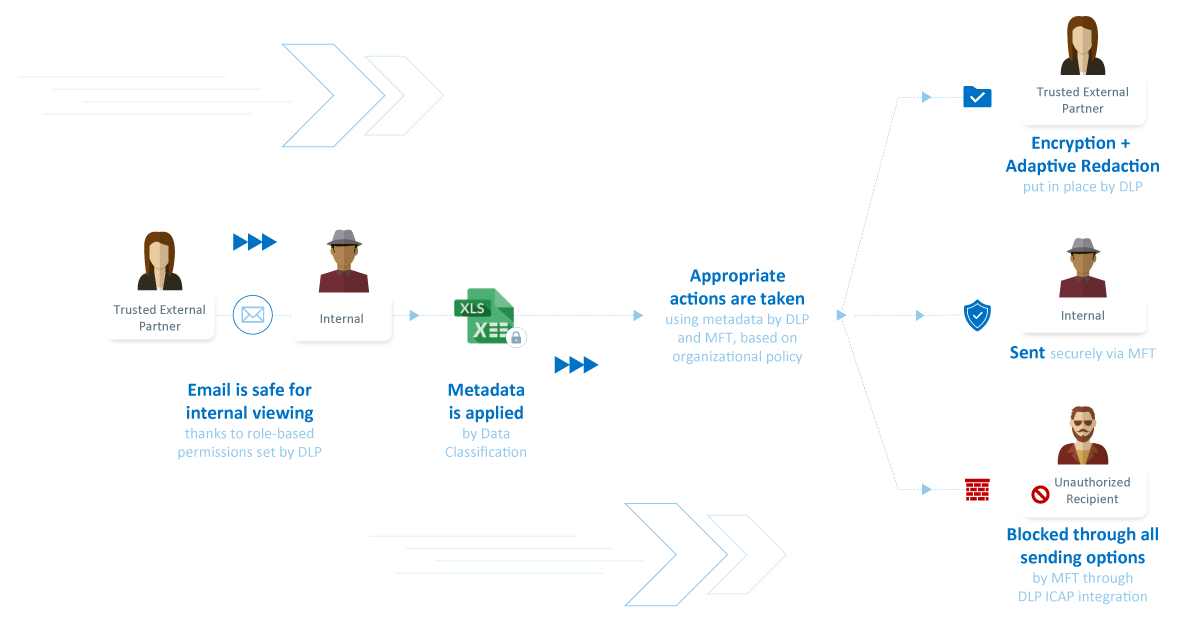
In this example use case, a trusted external partner sends an email which is vetted and approved for internal viewing. An internal employee then classifies and shares data securely with another trusted external partner, but some of that data is redacted. When someone attempts to share the file with an unauthorized recipient, the action is blocked.
Understand and Classify
Before data can be shared, it must be discovered, classified, and protected appropriately. Whether your critical data is intellectual property, PII, or other sensitive data, our data protection solutions identify and classify the data, classify it, handle it according to policy, block threats, and ultimately wrap the data in protection so wherever it is shared, it will remain in the right hands.
Detect and Prevent
Minimize the risk of a data breach by automatically removing sensitive data from emails and documents as they are sent or transferred to and from the cloud. Our email security solutions provide an additional layer of real-time sanitization to protect your organization from phishing, ransomware, business email compromise, and other Advanced Persistent Threats.
Secure and Protect
Our secure file transfer and digital rights management solutions secure and protect sensitive data through its entire life cycle, everywhere it travels, no matter its size, who has it, or where it’s stored. We help you protect confidential data at the point of its greatest vulnerability— when it’s being used by others, and while it travels outside your perimeters into unmanaged domains, devices, and applications. We do this by attaching encryption, security, and policy directly to the data itself, giving security practitioners and IT teams the power to control it. Then finally, digital risk protection solutions help you safeguard your critical assets even further by providing expert-curated threat intelligence and mitigation services.
Let Us Help Protect Your Data
Ready to add layers of protection to your data security defense? Contact us today.

About Fortra
Fortra is a people-first software company focused on helping exceptional organizations Build a Better IT™. Our holistic suite of security and automation solutions create a simpler, smarter, and more powerful IT. With customers in over 100 countries and across all industries, organizations everywhere trust Fortra to provide peace of mind. Learn more at www .fortra.com.