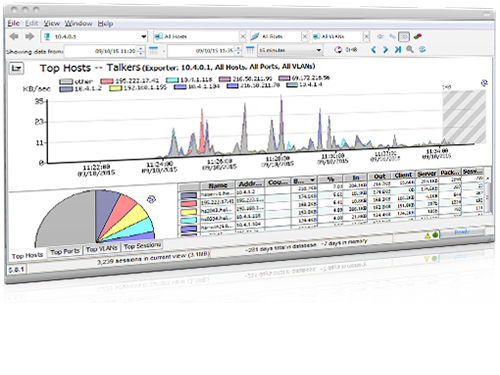
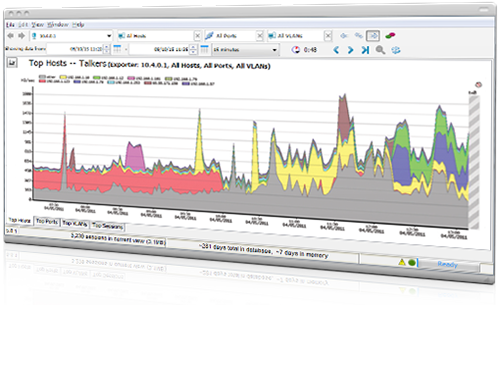
Reliable NetFlow monitoring software shows you top talkers and listeners for clear answers about traffic flow
With increased stress on your network, can you easily identify which machine, application, or user is consuming all the bandwidth? Getting visibility into NetFlow traffic, including top talkers, traffic statistics, and application types, helps you resolve network issues faster and keep traffic flowing.
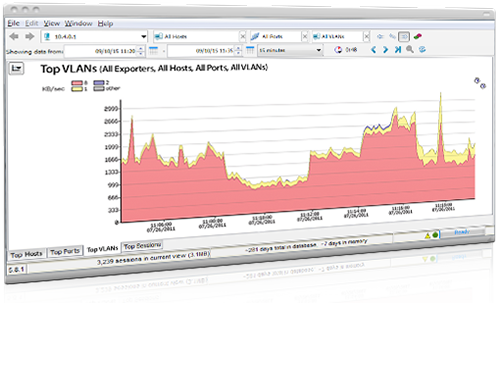
Intermapper Flows collects and exports NetFlow, Jflow, and sFlow data, then graphs it for easy analysis of traffic flowing across your network. Used with Intermapper, Intermapper Flows makes it easy to dig into suspicious spikes or dips in bandwidth usage.
Capabilities of Intermapper Flows
Get the full picture on network usage—past and present. Solve network issues quickly. Make data-driven decisions. With Intermapper Flows, you can:
Benefits of Intermapper Flows
Comprehensive NetFlow Analyzer & Monitoring Software
You need to know the type, origin, and behavior of traffic that's flowing across your network at all times. Having data on both real-time and historic network traffic helps you troubleshoot issues, plan for future IT needs, and prove compliance.
Intermapper Flows collects real-time NetFlow data and stores it over time, making it easy for you to analyze traffic patterns. All conversations passing through your network are recorded and saved for future reference so you have the full picture of how the network's performing.
Read More: The Importance of Bandwidth Monitoring
NetFlow, sFlow, jFlow, and cFlow Analysis
View detailed traffic information in seconds with a real-time NetFlow analyzer. Intermapper Flows gives you the ability to monitor NetFlow, sFlow, jFlow, and cFlow right from the Intermapper interface.
With a network traffic monitoring tool like Intermapper Flows, you can instantly identify:
- Top Talkers, Hosts, and Listeners
- Most frequently visited websites
- Download data
- Which IP addresses are connected to a large number of hosts
Real-Time Flow Monitoring
Intermapper already monitors your network in real time. With Intermapper Flows, those live metrics are collected with sub-millisecond accuracy to create a complete picture of network traffic.
Simply click into your network map for data on traffic origins and high-level summaries of key metrics. Break out collected data for thorough analysis by application, conversation, domain, endpoint, protocol, and more.
Start a Free Trial
As powerful bandwidth monitoring software, Intermapper Flows gives you a complete picture of network activity. Try it free for 30 days when you download Intermapper.
Interested in adding NetFlow monitoring to your Intermapper installation? We can tell you how many exporters you’ll need based on your current network configuration.
