How serious are insider threats on IBM i?
We all want to trust the users on our systems. Most have been around for years and they're loyal employees.
But on every platform, users with too much access and not enough oversight pose a risk to mission-critical data and applications. IBM i is no different.
All too many organizations have learned the hard way: failing to manage user IDs and access is a disaster in the making.
Image
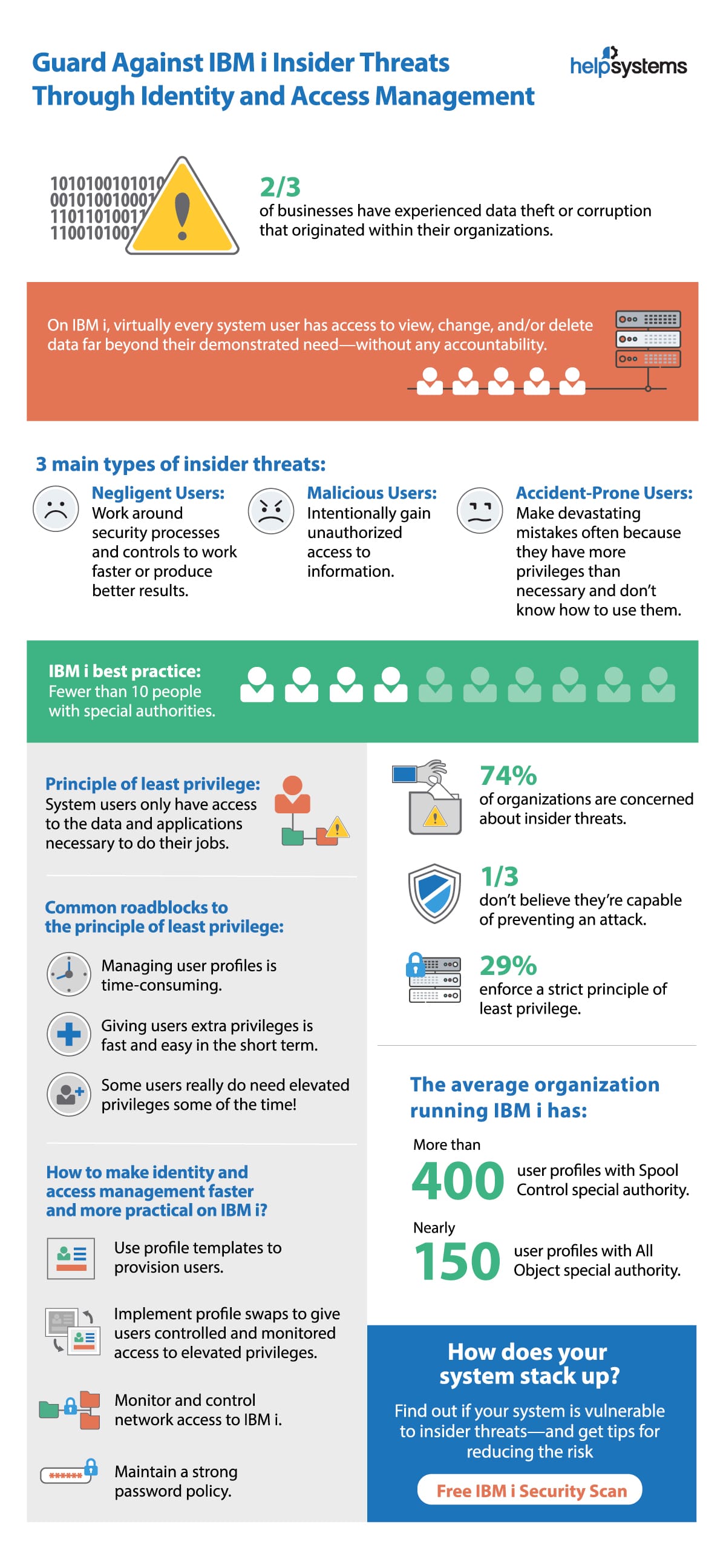
How Vulnerable Is Your System?
Find out if your users have too much access and not enough accountability. Request a free IBM i Security Scan to learn where your system is secure where it's at risk.