
Do your users have ODBC connections to your IBM i environment through tools like Microsoft Access or Microsoft Excel?
Unprotected ODBC connections make it easy for people to access unauthorized data or accidentally change and delete database records.
Surveyor/400 minimizes the risk of unauthorized access by providing connections to your IBM i data while maintaining database security and integrity. A user must specify a valid IBM i User ID and password within the product to connect to an IBM i system. Any existing user authorities in your environment are still honored; if a user isn’t authorized to an object on the system, they won’t be able to access it through Surveyor/400.
Role-Based Access
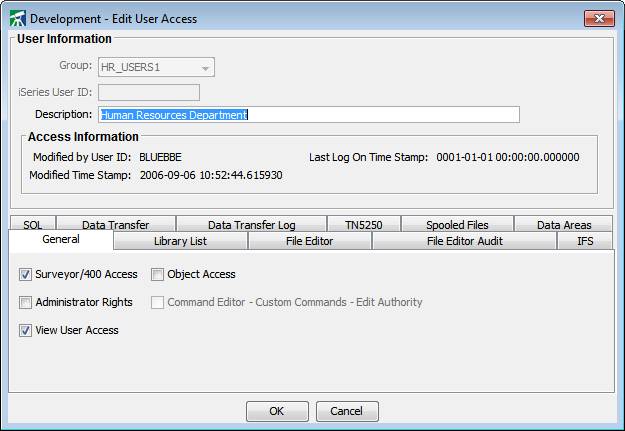
In addition to normal IBM i security, Surveyor/400 allows administrators to further restrict users (or groups of users) to specific product features, libraries, database files, database file fields, and database file records.
All connections to databases and any work done through the terminal emulator in Surveyor/400 can be protected using SSL. Securing your connections not only helps meet security policies, it prevents anyone from gaining access to resources through unsecured connections.
Each IBM i machine (or LPAR) is configured with its own user authority settings. An administrator can, for instance, grant a user access rights to modify database records on a development box but restrict them from modifying database records on a production machine.
Quick Details
- Allow Surveyor/400 administrators to grant/deny features for other users
- Restrict access to Surveyor/400 product
- Set the library list for a User ID - user is then restricted to those libraries if checkmark is removed from the Modify Library option
- Restrict access to running commands
- Set security limits for the File Editor
- Create an audit trail to log any records that a user adds, changes, or deletes through the File Editor
- Limit access to IFS options, SQL security, Data Transfer security, and more
Get Started
Find out how Surveyor/400 can help you maximize the value of your IBM i. Sign up for a free trial today.